Configure External OAuth for Snowflake Connections
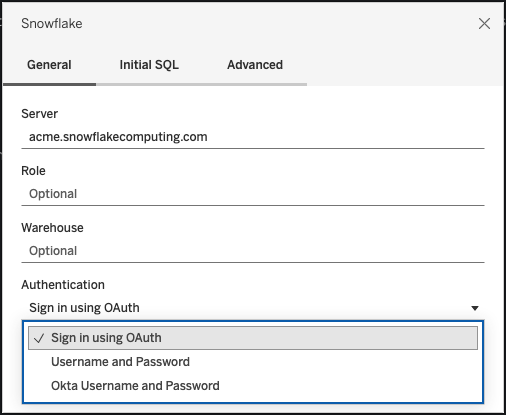
When you connect to your Snowflake data, you have three authentication options to choose from.
OAuth: You can use OAuth to enable federation from an IDP.
Okta Username and Password: You can embed the IDP credentials in the connection (only for Okta).
Username and Password:User credentials are stored in Snowflake.
Usually, we recommend using OAuth. This option offers the best combination of functionality and security.
With OAuth, you can:
- Use an identity provider (IdP) to facilitate access.
- Configure it to provide a single sign-on (SSO) experience.
- Enforce multi-factor authentication (MFA).
OAuth 2.0 is an industry-standard protocol for authorization.
Note: Be careful not to confuse this with Tableau’s SAML IdP authentication option in the connection dialog. You should connect using the Sign-in using OAuth option.
When you use OAuth, a key consideration is keeping access for content published to Tableau Server or Tableau Cloud. When Tableau content connects live to Snowflake via OAuth, owners must reauthenticate the workbook connection each time the access token expires (every 90 days by default).
See the Snowflake help topic, Configure Snowflake OAuth for Partner Applications(Link opens in a new window), for details on setting the access token expiration limit. If you have a business need to extend this period to prevent errors on your Tableau content, contact Snowflake Support(Link opens in a new window) for assistance. If you don’t manually refresh your content before this time period, it can cause an error when the Tableau workbook tries to load.
Configure OAuth between Snowflake and Tableau
When creating a connection between Tableau and Snowflake, both must have OAuth configured.
- Tableau: Tableau includes credentials for Snowflake to allow access. This happens automatically when you use the Snowflake connector in Tableau Cloud and Tableau Desktop, as well as Tableau Server versions 2023.3 and older, so no additional OAuth configuration is required. For more information on configuring Tableau Server in version 2024.2 and beyond, see Configure Oauth for Snowflake Connections in Tableau Help.
- Snowflake:
- For Tableau Desktop and Tableau Cloud, as well as Tableau Server versions 2023.3 and older, you'll configure partner integrations for Snowflake(Link opens in a new window).
- For Tableau Server versions 2024.2 and beyond, you'll need to configure a custom client integration for Snowflake OAuth(Link opens in a new window).
- For Tableau versions 2024.3 and beyond, you can configure a 3rd party IdP (external OAuth) for Snowflake. For more information, see External OAuth for Snowflake.
Note: Beginning with Tableau Serverversion 2020.4, your OAuth connection can use AWS PrivateLink or Azure Private Link. For more information, see Configure OAuth for Snowflake Connections(Link opens in a new window).
About using SSO with OAuth
Single Sign-On (SSO) adds another layer of security on top of OAuth authentication. A separate IdP configured for SSO manages authentication for all access activity across applications for your organization. All sign-in requests are routed to the SSO server, which displays a common sign-in dialog and checks the user’s credentials against a centralized database.
Tip: You can use saved credentials to avoid getting reprompted for your password. For more information, see Manage Saved Credentials for Data Connections(Link opens in a new window).
Configure OAuth between Okta and Snowflake
|
Snowflake uses Okta as the default identity provider (IdP) that provides access tokens and authenticates identities. You’ll need to configure settings in Snowflake and Okta for OAuth and single sign-on (SSO) capabilities. In Okta, you’ll define Okta as an OAuth authentication server and identify Snowflake as an OAuth resource. Follow the steps in this Snowflake help topic: Configuring an Identity Provider for Snowflake(Link opens in a new window). |

|
About using MFA with OAuth
Multi-factor authentication (MFA) introduces yet another layer of security. It needs two or more different methods of identification before the user can access a resource. Methods might include:
- A password
- A token from a second device
- Biometrics (fingerprint or eye scan, for example)
- Answer to a security question
You can optionally set up multi-factor authentication (MFA) with Okta or an other IdP for your connections between Tableau and Snowflake. For more on configuring MFA with Okta, see Okta Help(Link opens in a new window).
Other connection options
When you connect to Snowflake from Tableau Desktop, you have two other options:
|
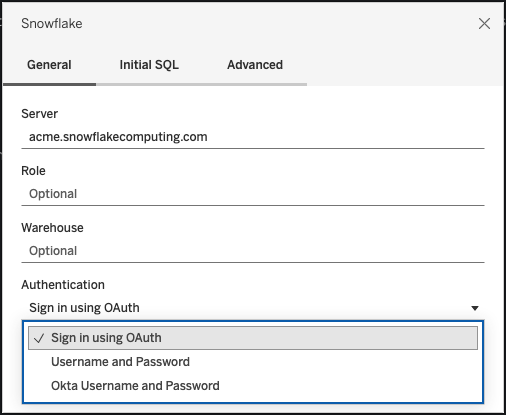
|
The Okta Username and Password option works only if Okta is your identity provider and if MFA is disabled for users in Okta. The Okta Username and Password option supports SSO but doesn’t support MFA. In this case, publishing with embedded credentials will use a specific user, but you can't employ per-user "viewer credentials" when you use Okta SAML.
If you select the Okta Username and Password authentication option, you will need to provide the URL for your Okta instance in the SAML Idp text field. This is passed to the driver as the authenticator. There are other options for this field, but when using Okta username and password authentication, we only support passing the IDP URL value. For more information, see the Snowflake documentation on federated authentication and SSO(Link opens in a new window).
In the past, some customers have used the “external browser(Link opens in a new window)” option with SAML IdP as a workaround to achieve SSO between Tableau Desktop and Snowflake. It won’t work for Tableau Server, Tableau Cloud, or Tableau Bridge. We recommend that you use the OAuth connection instead.
The Username and Password option uses the password stored by Snowflake. This option requires users to reauthenticate with their credentials whenever they connect to Snowflake or to embed these credentials.
Frequently asked questions
Why do my published Snowflake data extracts fail after a period of time?
It may be that your OAuth access token has expired. You’ll need to manually reauthenticate to the data source to refresh the token. If you need to extend the lifetime of these tokens in the future, you can contact Snowflake Support(Link opens in a new window).
How do I choose between "Prompt User" and "Embed Credentials" options when publishing a Snowflake data source?
If you would like any user accessing the data source to use their own credentials when connecting to the data source and associated content, use the Prompt User option. You can choose to embed credentials so everyone who accesses that data source uses those specific credentials. This method is functionally similar to using a "service account".
How do I use the row-level security that I've set up on Snowflake?
When users are prompted to enter their own credentials to access Snowflake from Tableau, those credentials map to the privileges they have in the Snowflake account.
See also
-
OAuth Connections — Learn more about OAuth support with Tableau.
-
OAuth (Snowflake Help) — Learn about Snowflake with OAuth.
-
Summary of Security Features (Snowflake Help) — Find information about how Snowflake supports OAuth, SSO, and other security features.
-
Manage Your Account Settings — Read about how to create and revoke personal access tokens.
