Personal Access Tokens
Personal access tokens (PATs) provide you and your Tableau Cloud users the ability to create long-lived authentication tokens. PATs enable you and your users to sign in to Tableau REST API without requiring hard-coded credentials (username and password) or interactive sign-in. For more information about using PATs with Tableau REST API, see Signing In and Out (Authentication)(Link opens in a new window) in the Tableau REST API Help.
This topic discusses how to configure and use PATs with Tableau Cloud sites. For information about how to use PATs with Tableau Cloud Manager, see Personal Access Tokens for Tableau Cloud Manager.
We recommend creating PATs for automated scripts and tasks that are created with the Tableau REST API:
-
Improve security: PATs reduce risk in the event credentials are compromised. Instead of using a user name and password, users can reduce the impact of credential compromise by using a personal access token for automated tasks. If a PAT gets compromised or is used in automation that is failing or posing a risk, you or your users can just revoke the PAT instead of rotating or revoking the user's credentials.
-
Manage automation: A PAT can be created for each script or task that is run. This allows you and your users to silo and review automation tasks across your organization. Additionally, by using PATs, password resets or metadata changes (username, email, etc.) on user accounts do not disrupt automation as it would when credentials are hard-coded into the scripts.
-
Monitor usage: If you have Tableau Cloud with Advanced Management, as a site admin, you can review Activity Log to track which users are creating and revoking PATs, which PATs are being used, which PATs are being revoked and the sessions attached to them.
Notes:
- You must use a PAT, instead of user name and password, to make a REST API sign in request to Tableau Cloud with multi-factor authentication (MFA) enabled with Tableau authentication.
- PATs are not used for generic client access to Tableau Cloud.
- To use PATs with tabcmd, install the compatible version of tabcmd from https://tableau.github.io/tabcmd/.
- PATs are automatically revoked when a user's authentication method(Link opens in a new window) is changed.
Understand personal access tokens
When a personal access token (PAT) is created, it is hashed then stored in the repository. After the PAT is hashed and stored, the PAT secret is shown once to the user and then no longer accessible after the users dismisses the dialog. Therefore, users are instructed to copy the PAT to a safe place and to handle it as they would a password. When the PAT is used at run-time, Tableau Cloud compares the PAT presented by the user to the hashed value stored in the repository. If a match is made, then an authenticated session is started.
In the context of authorization, the Tableau Cloud session that is authenticated with a PAT has the same access and privileges as the PAT owner.
Note: Users can't request concurrent Tableau Cloud sessions with a PAT. Signing in again with the same PAT, whether at the same site or a different site, will terminate the previous session and result in an authentication error.
About PAT expiration
Personal access tokens (PATs) expire if not used after 15 consecutive days. If PATs are used more frequently than every 15 days, their expiration depends on the PAT's site setting, which is configurable by a site admin.
After PATs expire, they're unable to be used for authentication and removed from the user's My Account Settings page.
Site settings for personal access tokens
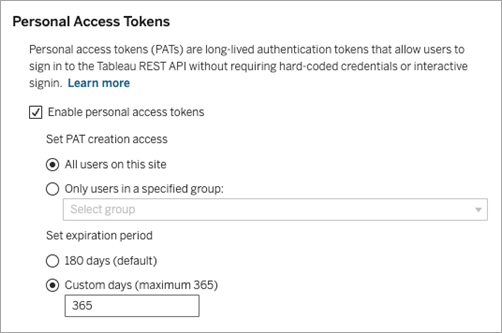
Configure PAT creation and expiration
As a site admin, you can configure who can create and use PATs, and when PATs expire. The changes that you make to PATs settings apply only to new PATs. PATs created before setting changes retain the configurations present when they were created and remain valid until they expire.
On sites activated in June 2023 (Tableau 2023.2) and later, creating PATs is disabled by default. On sites activated before June 2023 (Tableau 2023.2), creating personal access tokens (PATs) is enabled for all users by default and have a default expiration of one year.
-
Sign in to Tableau Cloud as a site admin and navigate to the Settings page.
-
Under the Personal Access Tokens section, select the Enable personal access tokens check box if not already selected, and do one of the following tasks:
-
Keep the Enable personal access tokens check box selection to enable all users to create PATs.
-
Alternatively, select the Only users in the specified group radio button and select a group from the list to limit the access of creating new PATs only to the users that are members of that group.
Note: If you select this option, a group must be selected in order for you to save the setting.
-
-
Under Set expiration period, do one of the following:
-
If not selected already, select the 180 days radio button.
-
Alternatively, in the Custom days text box, enter a valid value, 1 through 365.
-
-
When finished, click the Save button on the top or bottom of the page.
Tasks for managing users' personal access tokens
Create a PAT
Site admins can't create PATs for users. Your users must create their own PATs.
Users with accounts on Tableau Cloud can create, manage, and revoke personal access tokens on the My Account Settings page. For more information, see Manage Your Account Settings(Link opens in a new window) in the Tableau Help.
Note: A user can have up to 104 PATs.
Monitor PATs usage
If you have Tableau Cloud with Advanced Management, you can use Activity Log to monitor PATs usage. Events in the Activity Log that capture PATs usage include, but not limited to: issue token (issue refresh token), log in with token (login with pat), redeem token (redeem refresh token), and revoke token (revoke refresh token). For more information about these events, see Activity Log Site Event Type Reference.
Revoke a PAT
As a site admin, you can revoke a user's PAT. A user is also able to revoke their own PAT on their My Account Settings page using the procedure described in the Manage Your Account(Link opens in a new window) topic in the Tableau User Help.
-
Sign in to Tableau Cloud as a site admin and navigate to the Users page.
-
Locate the user whose PAT you want to revoke. For more information about navigating Server Admin pages and locating users, see View, Manage, or Remove Users.
-
Click the user's name to open their profile page.
-
On the user's profile page, click the Settings tab.
Note: A site admin can only access the Settings tab and see a user’s PAT if they are a site admin on all the sites that the user belongs to.
-
Under the Personal Access Tokens section, identify the PAT that you want to revoke and then click the Revoke Token button.
-
In the Delete dialog, click the Delete button.
